Technology Activation
Data is a vital part in the implementation of hc1 software solutions, and your IT resources have a significant stake in the project. A smooth activation is supported by an engaged and active team on both sides. By introducing your IT experts to our IT experts, we can ensure an activation that will go as smoothly and as quickly as possible.
Project Prep
IT Security Assessment
A security risk assessment (SRA) is a review of whether a proposed transfer of, access to and storage of sensitive data is consistent with an organization’s minimum security and privacy standards.
You will need to confirm with your IT team whether an SRA is required, and if so, what is required and when it needs to be completed. Additionally, if you are a multi-site organization, IT may require that separate assessments are completed for each site.
The earlier you can get in touch with IT and gather details the better – this will help hc1 prepare for the assessment in advance and move the purchasing process forward faster. We recommend you ask IT to send the SRA document to hc1 as soon as possible so our security and legal team can assist with the completion of these documents. We can typically complete them in 2-4 weeks.
hc1 is not only fully compliant with HIPAA, but we also meet the HITRUST CSF® Risk-based, 2-year (r2) certification criteria, placing hc1 in an elite group of organizations worldwide that have earned this certification.
An SRA typically asks for information about the following:

Your assistance with advising your IT team and other departments that the hc1 Platform®, as well as the policies,
processes and procedures supporting the platform and related operations, is HITRUST certified is key to an efficient purchasing process.
Connectivity
We offer various secure connection methods to ensure your organization can choose the option that best fits your security requirements and infrastructure. These options include both inbound connections to hc1 and outbound connectivity from hc1 to your customers’ sites.
For most customers, we recommend using a TLS connection, which provides encryption from end to end using standard protocols and procedures. The following sections provide an overview of TLS and our other available connectivity options.
Transport Layer Security (TLS)
TLS is a cryptographic protocol that provides secure communication over a computer network. It encrypts data transmitted between your systems and hc1.
Virtual Private Network (VPN)
A VPN establishes an encrypted tunnel between your network and hc1, providing a secure and private connection. If your source system is not able to create a TLS connection or otherwise encrypt the data, a VPN connection is a good option.
Mutual Transport Layer Security (mTLS)
In mTLS, a more advanced form of TLS, both the client and server authenticate each other using certificates. Enabling mTLS takes several steps. Please consult with your application provider for proper installation and use of an mTLS certificate.
Secure File Transfer (SFTP)
SFTP leverages encryption and authentication mechanisms to ensure that your data remains confidential and protected during transit. SFTP is particularly well-suited for scenarios where you regularly exchange large files or batches of data with hc1.
For more information on each connectivity option… click here!
When ready, a Connectivity request can be submitted through our Connectivity Portal:
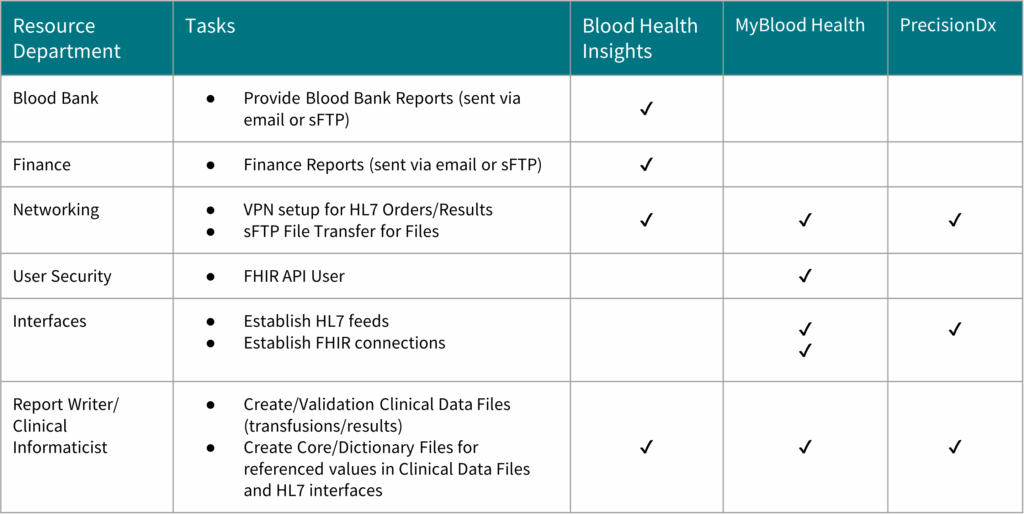
Resource Allocation
Securing the right expertise from the outset, allows for clear task alignment through the data delivery, which contributes to a streamlined and effective project delivery. Please note that while some of your team members may fulfill multiple roles, a successful activation will require each of these roles to be represented in different parts of the project.
What is my Role:
R = Responsible, A = Accountable, C = Consulted, I – Informed
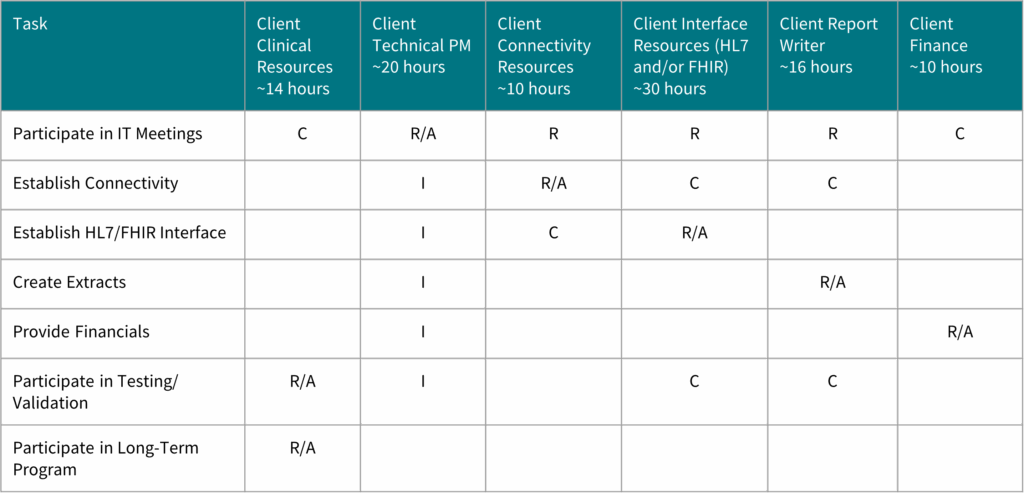
Resource estimates and involvement are based on standard activation best practices, though the number of resources, especially data analysts, may vary depending on project, customer needs, required business knowledge, and the number and familiarity with systems
Activation
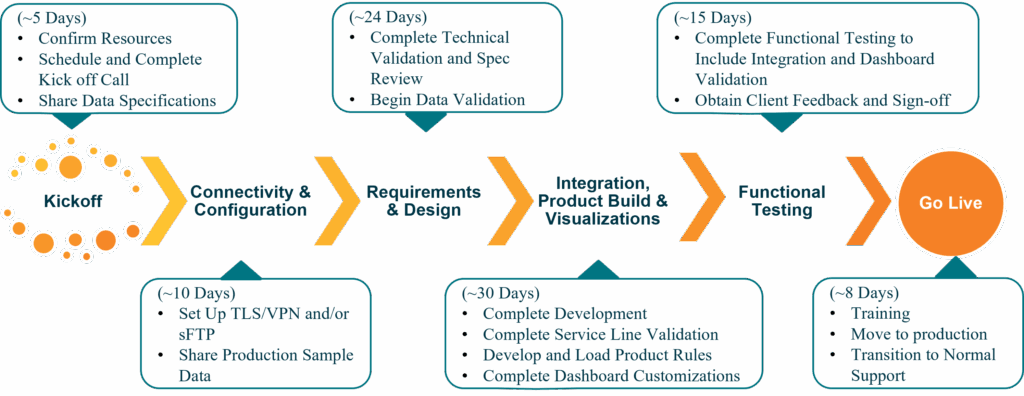
Our hc1 data requirements will be shared at the project kickoff. Accurate and comprehensive data flowing through to hc1 is essential for generating meaningful metrics. This data forms the foundation for tracking key performance indicators, identifying trends, and ultimately improving operational efficiency within your healthcare organization. Without robust and well-structured data, the ability to derive actionable insights from your metrics is severely limited.
What to Expect
Our Implementation delivery goal is to deliver the product within 90 days. We strive to make the process as easy as possible by using existing interfaces when available, driving a single project plan, raising roadblocks early and communicating often.
Post Go-Live
Support
Support services are provided with a Subscription to an hc1 Insights’ solution for customers under contract with hc1. For more information visit: https://hc1.com/support/
For optimal support and to maintain system integrity, we kindly request that only trained CRM administrators submit support tickets for hc1 products. This policy ensures that inquiries are handled by Client admin’s familiar with the customizable nature of our solutions and the protocols for managing Protected Health Information (PHI). This approach also helps us to efficiently address issues and uphold data security standards. Your Client CRM administrators may report issues or suspected bugs to us by contacting hc1 support as follows:
Phone: (317) 200-3720
email: hc1support@hc1.com
Support Form: hc1 Connect Support Form
Support Hours 9 am – 5 pm, Eastern Time, Business Days